NewStarCTF2023 Reverse Week3 EzDLL WP
分析
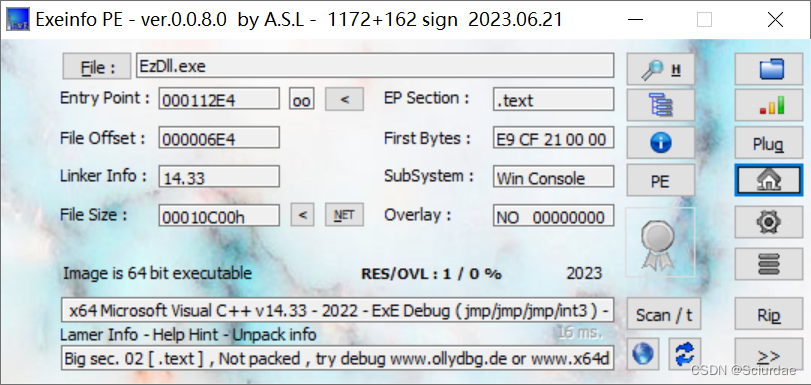
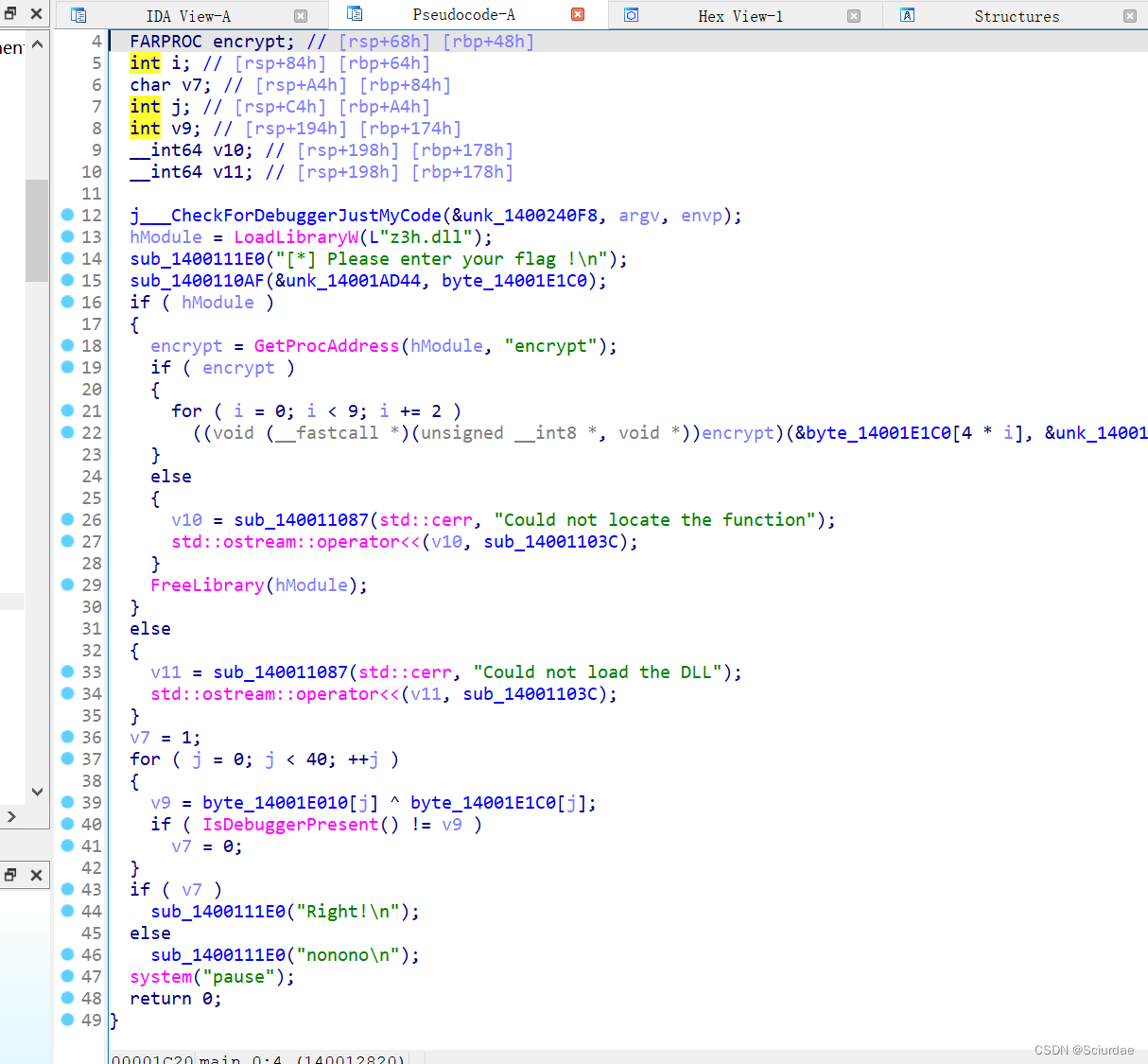
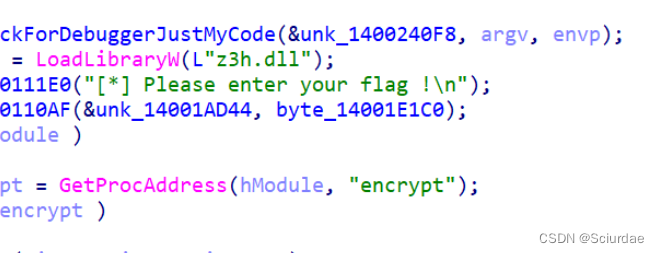
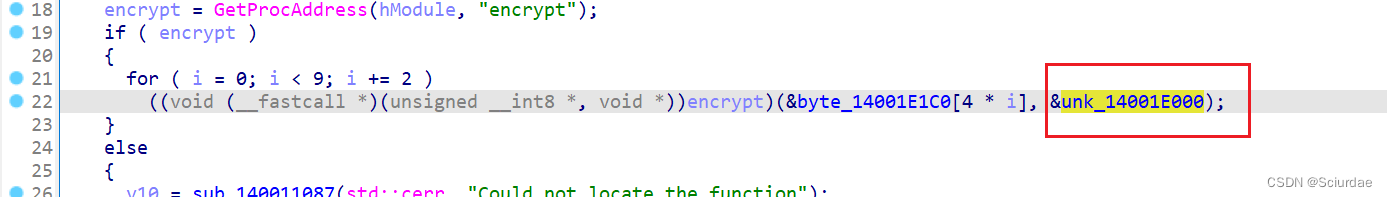
这里调用了z3h.dll中的encrypt函数。
用ida64载入z3h.dll
直接搜索encrypt

找到了一个XTEA加密。接着回去找key和密文。
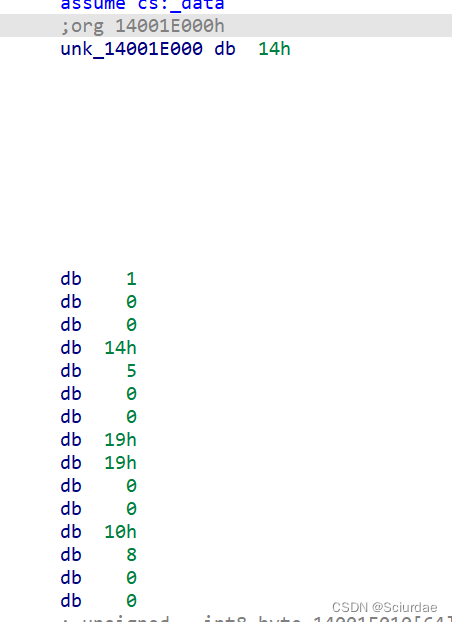
发现key

这里用了个调试状态来判断是否正确,v7=1,要v7=1才会输出Right,即程序要处于飞调试状态。
可以知道 这俩个字节数组要相同,这样v9才会=0;
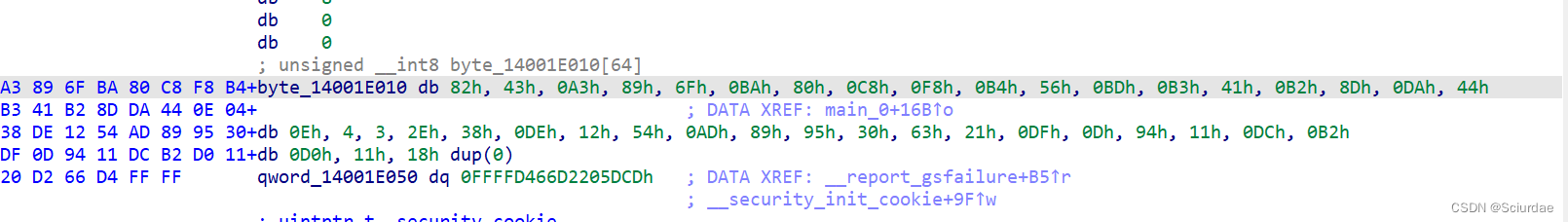
找到密文数据。。
EXP
#include <stdio.h>
void decrypt(unsigned int *v, unsigned int * key){
unsigned int v0 = v[0],v1 = v[1], sum = 0, delta = 0x3B9AC9FF;
sum = 1 + delta * 33;
for (size_t i = 0; i < 33; i++){
v1 -= (((v0 << 3) ^ (v0 >> 4)) + v0) ^ (sum + key[(sum >> 11 ) & 3]);
sum -= delta;
v0 -= (((v1 << 3) ^ (v1 >> 4)) + v1) ^ (sum + key[(sum & 3)]);
}
v[0] = v0;
v[1] = v1;
}
unsigned char a[41] = { 0x82, 0x43, 0xA3, 0x89, 0x6F, 0xBA, 0x80, 0xC8, 0xF8, 0xB4,
0x56, 0xBD, 0xB3, 0x41, 0xB2, 0x8D, 0xDA, 0x44, 0x0E, 0x04,
0x03, 0x2E, 0x38, 0xDE, 0x12, 0x54, 0xAD, 0x89, 0x95, 0x30,
0x63, 0x21, 0xDF, 0x0D, 0x94, 0x11, 0xDC, 0xB2, 0xD0, 0x11};
unsigned int key[] = {5,20,13,14};
signed main(){
unsigned int *t = (unsigned int *)a;
for (int i = 0; i < 9; i += 2){
decrypt(t+i,key);
}
for (int i = 0; i < 10; i++){
printf("%c%c%c%c", *((char *)&t[i] + 0), *((char *)&t[i] + 1), *((char *)&t[i] + 2), *((char *)&t[i] + 3));
}
}
